3 Legislation, voluntary initiatives, and standards
There are various standards and EU legislation relevant for servers and data storage products. This section will describe the ones that are considered most relevant for elaboration of material efficiency requirements within the EU ecodesign framework.
The addressed legislation, voluntary measures and standards are:
Legislation:
- The ecodesign framework Directive and the Ecodesign for Sustainable Products Regulation (ESPR)
- Critical Raw Materials ACT (CRMA)
- The current ecodesign regulation for servers and data storage products
- Energy Efficiency Directive (EED)
- The ecodesign and energy labelling regulations for smartphones and tablets as examples of regulations with extended material efficiency requirements
- Product specific legislation: Batteries.
Voluntary measures:
- The EU GPP criteria (Green Public Procurement criteria) for servers, data storage and network equipment
- Taxonomy (Mandatory for some companies)
- EU Code of Conduct on Data Centre Energy efficiency
- Data Centers (DE-UZ 228) – Blue Angel
- Climate Neutral Data Centre Pact.
Standards
- EU material efficiency standards
- EN standards in the EN 303 800 series
- ITU standards especially relevant for servers and data storage products
- Data sanitation standards
- Development of standards to support 2019/424 (Mandates)
- Development of standards regarding Plastics recycling, and recycled plastics. Plastic (M/584).
There are various other EU legislations which are relevant for the material efficiency of servers and data storage products including among others the WEEE Directive
Directive 2012/19/EU of July 2012 on waste electrical and electronic equipment (WEEE) https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX:02012L0019-20180704
Directive 2011/65/EU of 8 June 2011 on the restriction of the use of certain hazardous substances in electrical and electronic equipment https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX:02011L0065-20160715
3.1 Legislation
3.1.1 The Ecodesign Directive and the Ecodesign for Sustainable Product Regulation (ESPR)
The EU Ecodesign Directive
Directive 2009/125/EC of the European Parliament and of the Council of 21 October 2009 establishing a framework for the setting of ecodesign requirements for energy-related products. https://eur-lex.europa.eu/legal-content/EN/TXT/PDF/?uri=CELEX:32009L0125
The Directive can be used for adoption of both energy efficiency requirements and requirements with regard to resource efficiency and circularity of products. While regulations adopted within the ecodesign framework in the beginning mainly focused on energy efficiency, the most recent regulations implement various detailed rules with regard to material efficiency.
The EU Commission are revising the Ecodesign Directive and published in March 2022 the proposal for a new Ecodesign for Sustainable Products Regulation (ESPR)
Proposal for a Regulation of the European Parliament and of the Council establishing a framework for setting ecodesign requirements for sustainable products https://eur-lex.europa.eu/legal-content/EN/TXT/PDF/?uri=CELEX:52022PC0142.
A link to the final adopted act was not available at the time of publishing this report.
Provisional agreement between European Parliament and the Council on ESPR: https://ec.europa.eu/commission/presscorner/detail/en/ip_23_6257
The ESPR extends the ecodesign framework in two ways: first, to cover the broadest possible range of products; and second, to broaden the scope of the requirements with which products are to comply.
The framework will allow for the setting of a wide range of requirements, including on:
- product durability, reusability, upgradability and reparability
- presence of substances that inhibit circularity
- energy and resource efficiency
- recycled content
- remanufacturing and recycling
- carbon and environmental footprints
- information requirements, including a Digital Product Passport.
The “Digital Product Passport” will provide information about products’ environmental sustainability. This information will be easily accessible by scanning a data carrier and it will include attributes such as the durability and reparability, the recycled content, or the availability of spare parts of a product. It should help consumers and businesses make informed choices when purchasing products, make it easier to repair or recycle products, and facilitate tracking substances of concern along the supply chain. It should also improve transparency about products’ life cycle impacts on the environment and help public authorities to better perform checks and controls.
Labelling can be introduced as well. The proposal also contains measures to end the destruction of unsold consumer goods, as well as expand green public procurement and provide incentives for sustainable products.
For groups of products that share sufficient common characteristics, the framework will also allow for setting horizontal requirements.
3.1.2 Critical Raw Materials Act
The EU adopted in December 2023 the Critical Raw Materials Act (final act not yet available per January 2024). The aim of the act is to ensure that the EU have access to a secure and sustainable supply of CRMs and enable the Europe to meet its 2030 climate and digital objectives
Proposal for a Regulation of the European Parliament and of the Council establishing a framework for ensuring a secure and sustainable supply of critical raw materials https://eur-lex.europa.eu/legal-content/EN/TXT/PDF/?uri=CELEX:52023PC0160. Final act not yest av
The act has the following general objectives:
- to strengthen the different stages of the European critical raw materials value chain
- to diversify the EU's imports of critical raw materials to reduce strategic dependencies
- to improve the EU capacity to monitor and mitigate current and future risks of disruptions to the supply of critical raw materials
- to ensure the free movement of critical raw materials on the single market while ensuring a high level of environmental protection, by improving their circularity and sustainability.
To achieve the general objective mentioned above the Regulation aims to:
- strengthen the different stages of the strategic raw materials value chain with a view to ensure that, by 2030, Union capacities for each strategic raw material have significantly increased so that, overall, Union capacity approaches reaches the following benchmarks:
- Union extraction capacity is able to extract the ores, minerals or concentrates needed to produce at least 10% of the Union's annual consumption of strategic raw materials, to the extent that the Union’s reserves allow for this
- Union processing capacity, including for all intermediate processing steps, is able to produce at least 40% of the Union's annual consumption of strategic raw materials
- Union recycling capacity, including for all intermediate recycling steps, is able to produce at least 25%
- diversify the Union's imports of strategic raw materials with a view to ensure that, by 2030, the Union's annual consumption of each strategic raw material at any relevant stage of processing can rely on imports from several third countries, none of which provide more than 65% of the Union's annual consumption
- improve the Union's ability to monitor and mitigate the supply risk related to critical raw materials
- ensure the free movement of critical raw materials and products containing critical raw materials placed on the Union market while ensuring a high level of environmental protection, by improving their circularity and sustainability.
More specific the regulation:
- sets out lists of strategic critical raw materials, to be reviewed at least every three years
- sets out a framework to strengthen the EU’s strategic raw materials value chain by selecting and implementing Strategic Projects, that will be eligible for streamlined permitting processes and facilitated access to financing opportunities, which will be also improved by better coordination (Chapter III of regulation)
- develops a mechanism for coordinated monitoring of critical raw materials supply chains and provides measures to mitigate supply risks. It sets out a framework for systematically monitoring critical raw materials supply risks at different stages of the value chains. It also sets out a framework for risk mitigation by coordinating strategic stocks for strategic raw materials, by requiring large importers and manufacturers to regularly audit their supply chains and facilitating the joint purchases of strategic raw materials (Chapter IV of Regulation).
- contains provisions for developing the circularity of critical raw materials markets and lowering the environmental footprint of critical raw materials (Chapter V of Regulation). This includes:
- setting rules for Member States to adopt and implement measures on circularity, in particular with regard to waste streams with high critical raw materials recovery potential
- setting rules for Member States and extractive waste operators to assess the potential to recover critical raw materials from extractive waste sites.
- requiring of information on the type and composition of permanent magnets incorporated in products as well as on their recycled CRM content.
- provides, following a dedicated assessment, for the introduction of minimum recycled content thresholds
- setting out rules for the recognition by the Commission of certification schemes related to the sustainability of critical raw materials.
- provisions regarding the declaration of the environmental footprint or critical raw materials placed on the EU market
- rules on free movement, conformity and market surveillance related to products incorporating permanent magnets and CRMs for which the environmental footprint has to be declared.
- provides a framework for cooperation on Strategic Partnerships with third countries related to raw materials and to achieve greater synergies between Strategic Partnerships and Member States’ cooperation with relevant third countries (Chapter VI of the Regulation).
- sets up a European Critical Raw Materials Board, composed of high-level representatives from the Member States and the Commission, which will chair the Board. The Board will provide advice to the Commission and assist with coordination, cooperation and information exchange to support the implementation of this Regulation. (Chapter VII of the Regulation).
In addition, the regulation includes various articles on penalties, monitoring progress and on carrying out an evaluation of the Regulation. It also establishes a common reporting for Member States related to different measures and contains an article ensuring that confidential information collected under this Regulation is handled in a consistent manner.
The regulation does also contain measures on recyclability of permanent magnets in several product groups, although for some reasons the list of product groups covered, does not include servers.
3.1.3 Ecodesign regulation for servers and data storage products
The ecodesign regulation for servers and data storage products (EU) 2019/424
Commission Regulation (EU) 2019/424 laying down ecodesign requirements for servers and data storage products https://eur-lex.europa.eu/legal-content/EN/TXT/PDF/?uri=CELEX:32019R0424
The material efficiency requirements in the ecodesign regulation deal with disassembly for repair and reuse of components, secure data deletion, availability of firmware and security updates, information requirement regarding content of cobalt in batteries and neodymium in HDDs (hard desk drives) and instruction on disassembly operations.
The requirement on the extraction of key-components is expected to foster the reparability and upgradability of servers and data storage products; nevertheless, the information on disassembly operations can be useful for other categories of stakeholders, such as the recyclers. The requirements are further described below.
The various information requirements apply from the time a product model is placed on the market until at least eight years after the placing on the market of the last product of a certain product model:
Disassemble for repair and reuse
Manufacturers shall ensure that joining, fastening, or sealing techniques do not prevent the disassembly for repair or reuse purposes of the following components, when present:
- data storage devices (including HDDs and SSDs)
- memory
- processor (CPU
- motherboard (main circuit board of the server)For the of the regulation, the motherboard includes connectors for attaching additional boards and typically includes the following components: processor, memory, BIOS (Basic Input/output system), and expansion slots.
- expansion card/graphic card
- PSU (power supply)
- chassis
- batteries.
Secure data deletion
A functionality for secure data deletion shall be made available for the deletion of data contained in all data storage devices of the product.
Availability of firmware and security updates
The latest available version of the firmware shall be made available from two years after the placing on the market of the first product of a certain product model for a minimum period of eight years after
the placing on the market of the last product of a certain product model, free of charge or at a fair, transparent, and non-discriminatory cost.
The latest available security update to the firmware shall be made available from the time a product model is placed on the market until at least eight years after the placing on the market of the last product of a certain product model, free of charge.
Information regarding security updates
The following information shall be available in the instruction manuals for installers and end-users (when present with the product), and on the free-access websites of manufacturers.
- information on the secure data deletion functionality, including instructions on how to use the functionality, the techniques used and the supported secure data deletion standard(s)
Information regarding content of CRMs
The following information shall be available free of charge to third parties dealing with maintenance, repair, reuse, recycling and upgrading of servers (including brokers, spare parts repairers, spare parts providers, recyclers and third-party maintenance) upon registration by the interested third party on a website:
- indicative weight range (less than 5 g, between 5 g and 25 g, above 25 g) at component level, of the following critical raw materials:
- Cobalt in the batteries
- Neodymium in the HDDs
Instructions on disassembly operations
The following information shall be available free of charge to third parties dealing with maintenance, repair, reuse, recycling and upgrading of servers (including brokers, spare parts repairers, spare parts providers, recyclers, and third-party maintenance) upon registration by the interested third party on a website:
- instructions on the disassembly operations for the components mentioned, including, for each necessary operation and component:
- the type of operation
- the type and number of fastening technique(s) to be unlocked
- the tool(s) required.
The regulation also includes information requirements related to the tested functionality of the products under declared operation condition classes (temperature and humidity) which indirectly addresses the durability:
- Information to be provided by manufacturers: declared operating condition class; it shall also be indicated that ‘This product has been tested to verify that it will function within the boundaries (such as temperature and humidity) of the declared operating condition class’.
Review clause
The review clause (Article 8) of the current regulation prescribes that the Commission shall assess the regulation and present the results to the Consultation Forum by March 2022. This deadline has not been met but a review study was initiated in the beginning of 2023 (ICF, n.d.)
Link to the homepage of the review study: https://eco-servers-review.eu/
With regard to circular economy the review study shall address in particular the appropriateness of updating the material efficiency requirements for servers and data storage products, including the information requirements on additional critical raw materials (tantalum, gallium, dysprosium and palladium), taking into account the needs of the recyclers (European Commission, 2019).
3.1.4 Energy Efficiency Directive (EED)
The recently published revised EED
Directive (EU) 2023/1791 of the European Parliament and of the Council on energy efficiency https://eur-lex.europa.eu/legal-content/EN/TXT/PDF/?uri=CELEX:32023L1791
- the name of the data centre, the name of the owner and operators of the data centre, the date on which the data centre started its operations and the municipality where the data centre is based
- the floor area of the data centre, the installed power, the annual incoming and outgoing data traffic, and the amount of data stored and processed within the data centre
- the performance, during the last full calendar year, of the data centre in accordance with key performance indicators about, inter alia, energy consumption, power utilization, temperature set points, waste heat utilization, water usage and use of renewable energy, using as a basis, where applicable, the CEN/CENELEC EN 50600-4 ‘Information technology – Data centre facilities and infrastructures’, until the entry into force of the delegated act adopted pursuant to Article 33(3).
An EU-level database will collect and publish data, which is relevant for the energy performance and water footprint of data centres with a significant energy consumption.
The reporting obligations are applicable from 15 May 2024 and every year thereafter. The EED also encourages that the contracting authorities make use of the core set of EU GPP criteria for data centres, server rooms, and cloud services. The obligations in the EDD are mainly dealing with energy performance of data centres.
In addition, Member States shall encourage owners and operators of data centres in their territory with a power demand of the installed IT equal to or greater than 1 MW to consider the best practices referred to in the most recent version of the European Code of Conduct on Data Centre Energy Efficiency.
Furthermore, contracting authorities and contracting entities that purchase data centres, server rooms and cloud services shall regarding energy efficiency of the product or service, make their best efforts to purchase only products and services that respect at least the technical specifications set at ‘core’ level in the EU GPP criteria for data centres, server rooms and cloud services.
3.1.5 Ecodesign regulations for mobile phones, cordless phones, and tablets
The ecodesign regulations for mobile phones, cordless phones and tablets (in the following smartphones and tablets)
Commission Regulation (EU) 2023/1670 laying down ecodesign requirements for smartphones, mobile phones other than smartphones, cordless phones and slate tablets. https://eur-lex.europa.eu/legal-content/EN/TXT/PDF/?uri=CELEX:32023R1670
The resource efficiency requirements in the ecodesign regulation include, among others:
- requirement for the availability of spare parts and access to repair and maintenance information
- spare parts shall be available for seven years after the date of end of placement on the market
- information on prices of spare parts (not seen in other regulations so far)
- detailed requirements regarding disassembly regarding fastener types (fasteners shall be removable, reusable or resupplied – for batteries resupplied or reusable),
- required tools, working environment and skills) and for preparation for reuse
- requirements for replacement of serial parts (not seen before in ecodesign regulations)
- detailed and new types of requirements regarding design for reliability (including requirements regarding drop resistance, scratch resistance, protection from dust and water ingress, reliability of buttons and switches, battery endurance, battery management, and operating system updates
- marking of plastic components
- recyclability requirements (access to dismantling information, including the sequence of dismantling steps, tools or technologies needed to access the targeted components).
- requirement for information in technical documentation and on free-access website of the manufacturer including:
- compatibility with removable memory cards, if applicable
- information regarding content (indicative weight range) of critical raw materials and environmentally relevant materials
- recyclability rate
- the percentage of recycled content for the product or a part thereof, where available.
Information to be made available in instructions and in user manuals on a free-access website of the manufacturer:
- how to access, via the device, information about the battery management system
- instructions for optimal battery maintenance
- where the package does not include a charger, the following information “For environmental reasons this package does not include a charger. This device can be powered with most USB power adapters and a cable with USB Type-C plug.”
Information to be shown on the display of the smartphone:
- that data encryption is enabled by default in the course of configuring a new device, including an explanation that this facilitates data erasure through factory reset
- If wireless charging is selected, a message notifying the user that wireless charging will likely increase the energy consumed the charging of the battery.
Some of the requirements are very product-specific, but a number of them are of a more general/horizontal nature and could also be applied to other products with similar characteristics. Some of these are described below. For more details, please refer to regulation 2023/1670.
Disassembly requirements
The regulation includes very detailed requirements regarding disassembly, as summarized below:
From 20 June 2025 manufacturers, importers, or authorized representatives shall ensure that the process for replacement of available parts meets the following criteria:
For spare parts available to professional repairers and for the display assembly:
- fasteners shall be removable, reusable or resupplied
- the process for replacement shall be feasible in at least one of the following ways:
- with no tool, with a tool or a set of tools that is supplied with the product or spare part, or with basic tools
- with commercially available tools.
- the process for replacement shall, as a minimum, be able to be carried out in a workshop environment
- the process for replacement shall, as a minimum, be able to be carried out by a generalist.
For spare parts available to professional repairers and end-users, with the exception of the battery or batteries:
Manufacturers, importers, or authorized representatives shall ensure that the process for replacement of parts meets the following criteria:
- fasteners shall be removable, reusable or resupplied
- the process for replacement shall be feasible with no tool, with a tool or a set of tools that is supplied with the product or spare part, or with basic tools
- the process for replacement shall be able to be carried out in a use environment
- the process for replacement shall be able to be carried out by a layman.
For batteries:
Manufacturers, importers, or authorized representatives shall ensure that the process for battery replacement meets the following criteria:
- fasteners shall be resupplied or reusable
- the process for replacement shall be feasible with no tool, with a tool or a set of tools that is supplied with the product or spare part, or with basic tools
- the process for replacement shall be able to be carried out in a use environment
- the process for replacement shall be able to be carried out by a layman.
or, as an alternative to the above points, ensure that the process for battery replacement meets the following criteria:
- fasteners shall be removable, reusable or resupplied
- the process for replacement shall be feasible in at least one of the following ways:
- with no tool, with a tool or a set of tools that is supplied with the product or spare part, or with basic tools
- with commercially available tools.
- the process for replacement shall, as a minimum, be able to be carried out in a workshop environment
- the process for replacement shall, as a minimum, be able to be carried out by a generalist
- the battery endurance in cycles achieves a minimum of 500 full charge cycles, and after 500 full charge cycles the battery must, in addition have, in a fully charged state, a remaining capacity of at least 83% of the rated capacity
- the battery endurance in cycles achieves a minimum of 1000 full charge cycles, and after 1000 full charge cycles the battery must, in addition have, in a fully charged state, a remaining capacity of at least 80% of the rated capacity
- the device is at least dust tight and protected against immersion in water up to one meter depth for a minimum of 30 minutes.
Requirements for preparation for re-use
Manufacturers, importers, or authorized representatives shall ensure that devices:
- encrypt by default, using a random encryption key, the user data stored in the internal storage of the device
- include a software function that resets the device to its factory settings and securely erases by default the encryption key and generates a new one
- record the following data from the battery management system in the system settings or another location accessible to end-users:
- Date of manufacture of the battery
- Date of first use of the battery after the set-up of the device by the first user
- Number of full charge/discharge cycles (reference: rated capacity)
- Measured State of Health (remaining full charge capacity relative to the rated capacity in %).
Requirements for serialised parts
From 20 June 2025 or from one month after the date of placement on the market, whichever is later, manufacturers, importers or authorized representatives shall, at least until 7 years after the date of end of placement on the market:
- In case the parts to be replaced by spare parts referred to in point 1(a) are serialised parts, provide non-discriminatory access for professional repairers to any software tools, firmware or similar auxiliary means needed to ensure the full functionality of those spare parts and of the device in which such spare parts are installed during and after the replacement
- In case the parts to be replaced by spare parts referred to in point 1(c) are serialized parts, provide non-discriminatory access for professional repairers and end-users to any software tools, firmware or similar auxiliary means needed to ensure the full functionality of those spare parts and of the device in which such spare parts are installed during and after the replacement
- Provide, on a free access website of the manufacturer, importer or authorized representative, a description of the procedure for the notification and authorization of the intended replacement of serialized parts by the owner of the device referred to in point (d); the procedure shall allow for remotely providing the notification and authorization
- Before providing access to the software tools, firmware or similar auxiliary means referred to in points (a) and (b), the manufacturer, importer or authorized representative may only require to have received a notification and authorization of the intended part replacement by the owner of the device. Such notification and authorization may also be provided by a professional repairer with the explicit written consent of the owner
- Manufacturers, importers or authorized representatives shall provide access to the software tools, firmware or similar auxiliary means referred to in points (a) and (b) within 3 working days after having received the request and, where applicable, the notification and authorization referred to in point (d)
- The access to the software tools, firmware or similar auxiliary means referred to in point (a) may, as regards professional repairers, be limited to professional repairers registered in accordance with points 2(a) and (b).
Design for reliability
The reliability requirements include the following issues (for further description see Annex II, B, 1.2 of the regulation):
- Drop resistance
- Scratch resistance
- Protection from dust and water ingress (using the IP codes)
- Battery endurance in cycles
- Battery management
- Operating system updates.
The requirements regarding battery endurance, battery management and operating system updates are considered of particular relevance for other products containing batteries and operative systems.
Marking of plastic components
Plastic components heavier than 50 g shall be marked by specifying the type of polymer with the appropriate standard symbols or abbreviated terms set between the punctuation marks ‘>’ and ‘<’ as specified in available standards. The marking shall be legible. Plastic components shall be exempt from marking requirements provided the following conditions are fulfilled:
- the marking is not possible because of the shape or size
- the marking would impact on the performance or functionality of the plastic components
- marking is technically not possible because of the moulding method.
For the following plastic components, no marking shall be required:
- packaging, tape, labels and stretch wraps
- wiring, cables and connectors, rubber parts and any other component where not enough appropriate surface area is available for the marking to be of a legible size
- PCB assemblies, PMMA boards, optical components, electrostatic discharge components, electromagnetic interference components, speakers
- transparent parts where the marking would obstruct the function of the part in question.
The proposed requirement for marking plastic is in line with the current requirements for electronic displays.
Information requirements
The proposed information requirements include some new elements compared to current regulations. These are as follows:
Information about CRM content
Manufacturers, importers, or authorised representatives shall provide in the technical documentation and make publicly available on free access websites the following information:
- indicative weight range of the following CRMs and environmentally relevant materials:
- Cobalt in the battery (weight range: less than 2 g, between 2 g and 10 g, above 10 g)
- Tantalum in capacitors (weight range: less than 0,01 g, between 0,01 g and 0,1 g, above 0,1 g)
- Neodymium in loudspeakers, vibration motors, and other magnets (weight range: less than 0,05 g, between 0,05 g and 0,2 g, above 0,2 g)
- Gold in all components (weight range: less than 0,02 g, between 0,02 g and 0,05 g, above 0,05 g).
Information regarding recyclability rate, percentage of recycled content and battery endurance
Manufacturers, importers, or authorised representatives shall provide, in the technical documentation and on publicly available, free-access websites, the following information:
- the indicative value of the recyclability rate Rcyc
- the indicative percentage of recycled content for the product or a part thereof, where available; if not available, the recycled content should be indicated as “not known” or “not available”
- minimum battery endurance in a number of cycles.
Ingress protection
Manufacturers, importers, or authorised representatives shall provide, in the technical documentation and on publicly available, free-access websites, the following information:
- ingress protection rating.
Information regarding batteries
User instructions in the form of a user manual, on a free-access website of the manufacturer, importer or authorised representative, shall include information regarding:
- how to access, via the device, information about the battery management system on:
- date of manufacture of the battery
- date of first use of the battery after the set-up of the device by the first user
- number of full charge/discharge cycles (reference: rated capacity)
- measured State of Health (remaining full charge capacity relative to the rated capacity in %).
- instructions for battery maintenance, including the following:
- impacts on battery lifetime related to exposure of the device to elevated temperatures, suboptimal charging patterns, fast charging and other known adverse factors
- effects of switching off radio connections, such as Wi-Fi, Bluetooth etc. on device power consumption
- information about whether the device supports other features which extend battery lifetime, such as smart charging, and about how these features are activated or under which conditions they work best.
Common chargers support
Where the package does not include a charger, the user instructions shall include the following information: “For environmental reasons this package does not include a charger. This device can be powered with most USB power adapters and a cable with USB Type-C plug.”
This requirement is relevant for all products placed on the marked with an external power supply.
3.1.6 Energy labelling of smartphones and tablets (regulation (EU) 2023/1669) Commission Delegated Regulation (EU) 2023/1669 with regard to the energy labelling of smartphones and slate tablets. https://eur-lex.europa.eu/legal-content/EN/TXT/PDF/?uri=CELEX:32023R1669
Commission Delegated Regulation (EU) 2023/1669 with regard to the energy labelling of smartphones and slate tablets. https://eur-lex.europa.eu/legal-content/EN/TXT/PDF/?uri=CELEX:32023R1669
For smartphones and slate tablets, an energy labelling regulation including circular economy aspects was published in August 2023. The layout and content of the energy label are shown in Figure 8. It is the first EU energy label including a reparability class on a scale from A to G based on a Repairability Index.
The reparability class of a smartphone or a slate tablet shall be determined on the basis of the repairability index. The most reparable being class A and the least reparable being class E, on a scale from A–E.
Reparability Class | Reparability Index (R) |
A (most raparble) | R ≥ 4,00 |
B | 4,00 > R ≥ 3,35 |
C | 3,35 > R ≥ 2,55 |
D | 2,55 > R ≥ 1,75 |
E (least reparable) | 1,75 > R ≥ 1,00 |
Table 6. Repairability classes of smartphones and slate tablets
The Repairability Index is calculated from six scoring parameters as follows:
R = (SDD*0,25) + (SF*0,15) + (ST*0,15) + (SSP*0,15) + (SSU*0,15) + (SRI*0,15)
where:
- SDD is the ‘Disassembly Depth’ score.
- SF is the ‘Fasteners (type)’ score.
- ST is the ‘Tools (type)’ score.
- SSP is the ‘Spare Parts’ score.
- SSU is the ‘Software Updates (duration)’ score.
- SRI is the ‘Repair Information’ score.
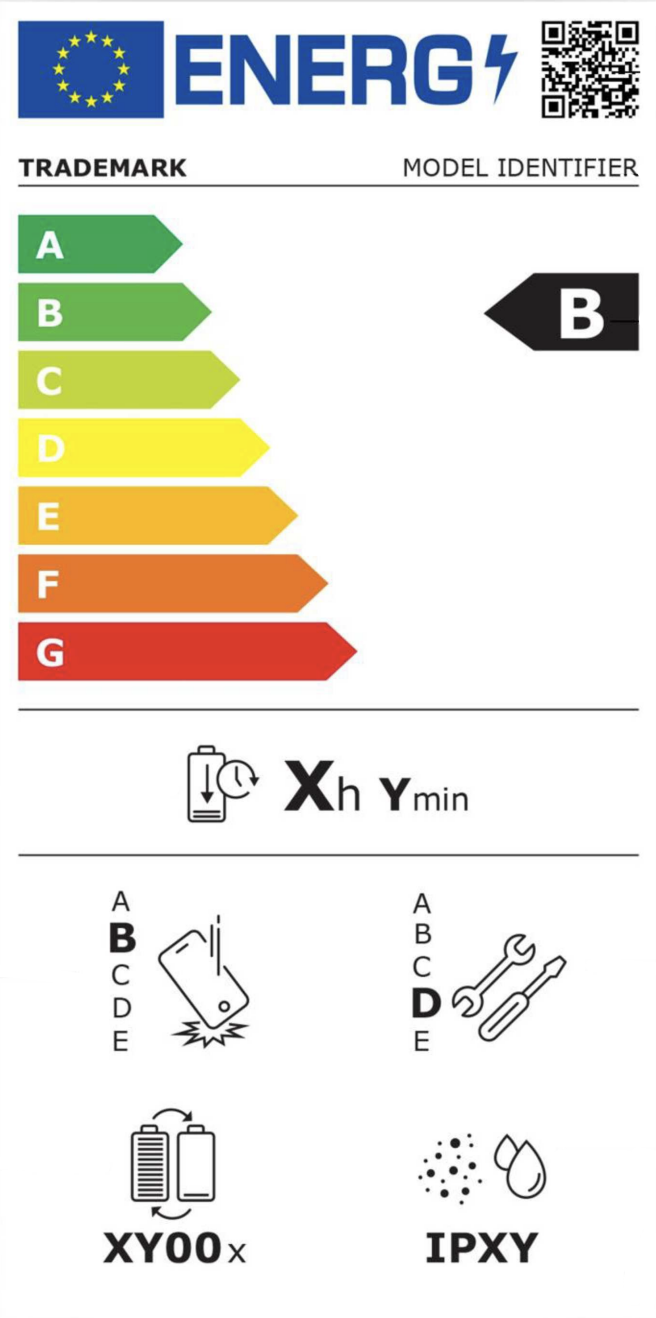
Figure 8. Layout of energy label for smartphones and slate tablets
The parameter that counts the most in the reparability index the score is the disassembly depth (DD). It shall be calculated based on the number of steps required to remove a part from a product, without damaging that product. Points ranging from 1 to 5 (the more steps the lower score). The points are assigned as follows:
DDi ≤ 2 steps = 5 pts
5 steps ≥ DDi > 2 steps = 4 pts
10 steps ≥ DDi > 5 steps = 3 pts
15 steps ≥ DDi > 10 steps = 2 pts
DDi > 15 steps = 1 pt.
For the calculation of disassembly steps, the following rules shall apply:
- the disassembly depth count is completed when the target part is separated and individually accessible
- where multiple tools need to be used simultaneously, the use of each tool counts as a separate operation. Operations related to cleaning, removing traces or heating are counted as steps
- where remote notification or authorisation of serial numbers is necessary for the full functionality of the spare part and the device, these actions are counted as additional disassembly steps.
For fasteners, 5 points are assigned to reusable fasteners, 3 points to resupplied fasteners and 1 point to removable fasteners.
For tools, points ranging 1 to 5 are assigned as follows:
- no tools = 5 pts
- basic tools = 4pts
- a set of tools that is supplied (or offered to be supplied at no additional cost) with the spare part = 3 pts
- a set of tools that is supplied (or offered to be supplied at no additional cost) with the product = 2 pts
- commercially available tools =1pt.
Points from 1 to 5 to are also assigned for spare part availability (more points if spare parts are also available to end-users), software updates (duration) and repair information.
The calculation methods needed for the establishment of label parameters are described in the proposed regulation. In addition, a tool for the calculation of the reparability index is provided in the regulation (see the section on transitional methods).
The parameters on the label could also be relevant for other product groups, especially other electronic products. Some could probably be applied horizontally but others would need product-specific adaptation.
Transitional methods are outlined in the proposed regulation in Annex IVa. The standard EN 45554:2020 is used as reference test method for fasteners (type) score (SF) and Tools (type) score (ST)
Product information sheet
The proposed regulation also requires that the supplier shall upload to the product database (EPREL) the information set out in the Product Information Sheet.
The user manual or other literature provided with the product shall clearly indicate the link to the model in the product database as a human-readable Uniform Resource Locator (URL), as a QR code or by providing the product registration number.
The Product Information Sheet shall include a variety of information, including the individual scores of the parameters used for the calculation of the repair score, maximum pre-tax price for various spare parts, list of spare parts available to professional repairers and to end-users respectively, number of falls without defects, battery endurance in cycles, ingress protection rating and screen scratch resistance.
3.1.7 Product specific legislation: Batteries
The Batteries Regulation (Regulation (EU) 2023/1542)
Regulation (EU) 2023/1542 of 12 July 2023 concerning batteries and waste batteries, https://eur-lex.europa.eu/legal-content/EN/TXT/PDF/?uri=CELEX:32023R1542
Starting from 2025, the Regulation will gradually introduce declaration requirements, performance classes and maximum limits on the carbon footprint of electric vehicles, light means of transport (such as e-bikes and scooters) and rechargeable industrial batteries.
The Batteries Regulation sets requirements on the content of harmful substances in batteries, which will be regularly reviewed. In addition, targets for recycling efficiency, material recovery and recycled content will be introduced gradually from 2025 onwards. All collected waste batteries will have to be recycled and high levels of recovery will have to be achieved, in particular of critical raw materials such as cobalt, lithium and nickel. This will guarantee that valuable materials are recovered at the end of the useful life of the battery and brought back in the economy by adopting stricter targets for recycling efficiency and material recovery over time.
Starting in 2027, consumers will be able to remove and replace the portable batteries in their electronic products at any time of the life cycle. This will extend the life of these products before their final disposal, will encourage re-use, and will contribute to the reduction of post-consumer waste.
Key data will be provided on a label, where a QR code will provide access to a digital passport with detailed information on each battery that will help consumers and especially professionals along the value chain in their efforts to make the circular economy a reality for batteries.
Under the new law’s due diligence obligations, companies must identify, prevent and address social and environmental risks linked to the sourcing, processing and trading of raw materials such as lithium, cobalt, nickel and natural graphite contained in their batteries.
3.2 Voluntary initiatives
3.2.1 EU GPP for data centres, server rooms, and cloud services
The EU has set voluntary green public procurement criteria (GPP criteria) for data centres, server rooms and cloud services which includes criteria for servers and data storage because these are main elements in data centres and server rooms (European Commission, 2020c).
The EU GPP criteria addresses various issues related to energy and material efficiency. The requirements regarding material efficiency are:
- Control of hazardous substances (Restricted Substance Controls RSCs) in servers, data storage and network equipment. The RSCs must apply, as a minimum, to the REACH candidate list of substances and Restricted substances and exemptions in the Restriction of Hazardous Substances Directive (criteria SC2).
- Design for repair and upgrading of servers and data storage (criteria TS 3)
- End-of-life management of servers, data storage and network equipment (criteria TS4)
The requirements on design for repair and upgrading are:
The tenderer must provide clear instructions to enable a non-destructive repair or replacement of the following components:
- data storage devices,
- memory
- processor (CPU)
- motherboard
- expansion cards/graphic cards
- power supply unit (PSU)
- fans
- batteries.
As a minimum, the instructions should include for each necessary repair operation and component:
- the type of operation
- the type and number of fastening technique(s) to be unlocked
- the tool(s) required.
The instructions must be made available to authorised third parties, including brokers, spare parts repairers, spare parts providers, recyclers, and maintenance providers via registration on the manufacturer's webpage. These instructions must be made available for a minimum of 8 years after the server product is placed on the market.
The above are to a large extent in line with the current ecodesign requirement for servers and data storage products, meaning that they are mandatory for products placed on or put into service in the EU.
The requirements on end-of-life management are:
Tenderers must provide a service for:
- The re-use and recycling of the whole product and/or
- The selective treatment of components in accordance with Annex VII of the WEEE Directive
- The recycling of components in order to recover Critical Raw Materials.
The service must comprise the following activities:
- Collection
- Confidential handling and secure data erasure (unless carried out in-house)
- Functional testing, servicing, repair and upgrading to prepare products for re-use
- The remarketing of products for re-use
- Dismantling for component re-use, recycling and/or disposal.
In providing the service, the tender must report on the proportion of equipment prepared or remarketed for re-use and the proportion of equipment prepared for recycling.
Preparation for re-use, recycling and disposal operations must be carried out in full compliance with the requirements in Article 8 and Annexes VII and VIII of the (recast) WEEE Directive 2012/19/EU and with reference to the list of components for selective treatment. See Figure 9.
Components requiring selective treatment in accordance with Annex VII of the WEEE Directive:
- mercury containing components
- batteries
- printed circuit boards greater than 10
- plastic containing brominated flame retardants, chlorofluorocarbons (CFC), hydrochlorofluorocarbons (HCFC) or hydrofluorocarbons (HFC), hydrocarbons (HC)
- external electric cables
- polychlorinated biphenyls (PCB) containing capacitors
- components containing refractory ceramic fibres
- electrolyte capacitors containing substances of concern
- equipment containing gases that are ozone depleting or have global warming potential (GWP) above 15
- ozone-depleting gases must be treated in accordance with Regulation (EC) No 1005/2009
Figure 9. Components requiring selective treatment according to WEEE.
Tenderers must also provide evidence of all the actions performed in order to improve the recycling of the Critical Raw Materials cobalt (in batteries) and of neodymium (in HDDs), in line with the available information on Cobalt and Neodymium content, as foreseen in Annex II.3.3.a to the Ecodesign Regulation (EU) 2019/424
This regulation was adopted in 2019 and the mentioned requirements have applied since 1 March 2020.
Verification:
The tenderer must provide details of the arrangements for collection, data security, preparation for re-use, remarketing for re-use and recycling/disposal. This must include, during the contract, valid proof of
compliance of the WEEE handling facilities to be used and the separation and handling of specific components that may contain Critical Raw Materials.
Operation condition range
In addition, the GPP document includes a criterion regarding operating condition range (temperature and humidity) which could be of importance for the lifetime/durability of servers and data storage equipment (criteria TS2).
Tenderers must also provide evidence of all the actions performed in order to improve the recycling of the Critical Raw Materials cobalt (in batteries) and of neodymium (in HDDs), in line with the available
information on Cobalt and Neodymium content, as foreseen in Annex II.3.3.a to the Ecodesign Regulation (EU) 2019/424
This regulation was adopted in 2019 and the mentioned requirements have applied since 1 March 2020.
Verification:
The tenderer must provide details of the arrangements for collection, data security, preparation for re-use, remarketing for re-use and recycling/disposal. This must include, during the contract, valid proof of
compliance of the WEEE handling facilities to be used and the separation and handling of specific components that may contain Critical Raw Materials.
3.2.1.1 Application of the GPP criteria
Experience of the Danish Agency for Digital Government
In 2022 the Danish Agency for Digital Government published an analysis of green public procurement of datacentres, server rooms and cloud services
Grønne datacentre, Danish Agency for Digital Government, 2022 (only available in Danish). https://digst.dk/media/26780/digitaliseringsstyrelsens-afrapportering-for-initiativ-om-groenne-datacentre.pdf
- Few public authorities set green requirements in tenders for data storage and processing, and the requirements that are set are very uneven, qualitative, and difficult to measure.
- Many public authorities would like to include green requirements but are worried about making too strict requirements and thereby risk limiting the field of suppliers.
On this background the Agency for Digital Government in a partnership with central, regional, or local authorities, has initiated a pilot testing of the application of the EU’s Green Public Procurement Criteria for data centers, server rooms and cloud service. The results should serve as a basis for decision-making for further implementation of green public procurement requirements for these products/services.
The preliminary experiences and observations of the pilot testing are that
Based on communication with Frederik Nøhr Brünner, Danish Agency for Digital Government.
- The GPP criteria are applicable in public tenders, e.g., because the criteria are linked to the subject of the contract and are based on objective criteria and standards, and the majority of the criteria are market compliant.
- The EU GPP criteria documents
- As a result of the ongoing testing and upcoming identical EU reporting requirements according to the revised Energy Efficiency Directive (see section 3.1.4) and the Taxonomy Regulation, a gradual maturation in the market is already visible and it is therefore expected that in 2024 the suppliers will be able to apply the criteria correctly.
The Agency for Digital Government concludes that the GPP’s is an important tool as it reduces complexity for both the purchasing authority and the supplier and thereby reduces both resource consumptions and burdens. In addition, the GPP creates an increased transparency as the criteria and methods for documentation and verification are based on well-established standards also referred to in other relevant EU legislation for instance EED, and Taxonomy Regulation. Apart from reducing supplier’s burdens, the use of identical standards and green requirements across GPP and other EU reporting requirements, also increases the supplier’s visibility and thereby supports investments in reducing the supplier’s products and services climate impact.
Experience of SKI
SKI (a centralized procurement body in Denmark) has in-depth experience with the use of GPP criteria for data centers, server rooms, and cloud services in several tenders (both framework agreements and dynamic purchasing systems). Their experience with the market and public procurers is that GPP is:
- Unclear/inadequate structure makes it very difficult to navigate through the criteria and identify the criteria relevant to the specific procurement.
- Confusing because the primary division/structure by Selection Criteria, Technical Specification, Award Criteria and Contract Performance Clauses is not helpful for a procurer, who needs to get a quick overview of relevant procurement criteria for their specific procurement as well as an overview of which requirements are related in content and possibly interrelated. Adding to this, the target audience experience an often unnecessarily complex language, with heavy use of technical terms and legal jargon, which deters use of the criteria.
- There is a lack of guidance around the individual criteria, which describes in a pedagogical way (for lay people) the object, purpose, substance and issues of attention of each criteria.
Whilst SKI agrees that the GPP is solid and relevant, the reality is that they are not used due – at least partly – to the above-mentioned obstacles.
In addition, SKI have identified the following questions to be critical for public procurers when they’re in the process of selecting green criteria – questions that the GPP criteria do not answer:
- Which green criteria can the market meet currently?
- How much more expensive is it to use a specific green criteria?
- Which of the criteria makes the biggest green impact?
In order to support public procurers in answering these essential questions, SKI has developed a new model for green criteria related to datacenters, which has been implemented in their 02.22 IT-services (a dynamic purchasing system). The model resembles an intersection (basic criteria, green light, yellow light and red light) as follows:
- Basic criteria (All suppliers can meet the criteria; not more expensive; supports the green agenda)
- Green (Most suppliers can meet the criteria; may be a little more expensive; supports the green agenda)
- Yellow (Few suppliers can meet the criteria; expected to be more expensive; supports the green agenda even more)
- Red (Very few suppliers can meet the criteria, costs may be significant; supports the green agenda a lot).
The tendering authority can freely choose which criteria they wish to use in their specific tender. In addition, SKI will once a year enter a dialogue with the suppliers on the system and the market to discover which criteria can be tightened whilst still following the methodology of the intersection -guidance. Criteria can thereby switch from, for example, red to yellow, yellow to green and so forth. Furthermore, in another tender from SKI (50.03 Server storage), SKI has used the GPP criteria as inspiration material for their award criteria of the framework agreement. Bidders were required to offer their “green services” in accordance with the GPP criteria’s focus areas. Ultimately this enables public procurers and IT-staff to gain in-depth support and guidance with regard to sustainability and the management of their server and storage solutions.
3.2.2 EU Code of Conduct on Data Centre Energy efficiency
The EU Code of Conduct (CoC) started in 2008 and is operated by the Joint Research Centre (JRC), part of the European Commission
Participants sign a registration form, through which they commit to conduct an initial energy audit to identify the major energy saving opportunities, prepare and submit an action plan and implement this plan according to the agreed timetable. Energy consumption must be monitored regularly to see overtime progress in the energy efficiency indicator related to the data centre. All Participants are required to follow the best practice guidelines (Acton et al 2021) which are updated annually, and to report annually. They have an obligation to continuously monitor energy consumption and adopt energy management in order to look for continuous improvement in energy efficiency. One of the key objectives of the CoC is that each participant benchmarks their efficiency over time, using the CoC metrics in order to produce evidence of continuous improvement in efficiency.
In addition, every year data centres that have adopted innovative technologies to improve their energy efficiency and have demonstrated outstanding improvements are given the Code of Conduct Data Centre Award. The criteria for the winners are the reduced need for mechanical cooling of the data centre for most of the time and raised indoor temperature. These are among the most important measures to improve efficiency and reduce energy consumption.
Energy efficiency targets expressed as PUE are complemented by general commitments to monitor power and energy consumption, adopt good management practices, increasing IT utilisation, switching off components not needed, and reducing energy consumption where possible.
The EU Code of Conduct does not include recommendations related to material content of the IT equipment used in the data centres. But section 3.2 General Policies include some general recommendations regarding energy efficiency and overall environmental impacts. Examples are:
- Consider the embodied environmental impact of installed devices
- Life Cycle Assessment
- Environmental Management
- Training and Development
3.2.3 Taxonomy RegulationEU Taxonomy Regulation (2020/852/EU) https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=celex%3A32020R0852 and delegated actCOMMISSION DELEGATED REGULATION (EU) 2021/2139 https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=celex%3A32021R2139
EU Taxonomy Regulation (2020/852/EU) https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=celex%3A32020R0852
COMMISSION DELEGATED REGULATION (EU) 2021/2139 https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=celex%3A32021R2139
The EU taxonomy is a classification system, establishing a list of environmentally sustainable economic activities. It is aimed at helping the EU scale up sustainable investment and implement the European green deal. The EU taxonomy would provide companies, investors and policymakers with appropriate definitions for which economic activities can be considered environmentally sustainable. In this way, it would contribute to create security for investors, protect private investors from greenwashing, help companies to become more climate-friendly, mitigate market fragmentation and help shift investments where they are most needed.
The EU Taxonomy Climate Delegated Act defines which economic activities most contribute to meeting the EU’s environmental objectives. It includes the activity storage, manipulation, management, movement, control, display, switching, interchange, transmission or processing of data through data centres, including edge computing, providing it complies with the EU Code of Conduct on Data Centre Energy efficiency.
The delegated act includes technical screening criteria for ‘do no significant harm’ for the economic activity “Data processing, hosting and related activities”. These criteria should ensure that the economic activity has no significant negative environmental impact. Relevant technical criteria for servers and data storage products are:
- The activity has implemented all relevant practices listed as ‘expected practices’ in the most recent version of the European Code of Conduct on Data Centre Energy Efficiency, or in CEN-CENELEC document CLC TR50600-99-1 ‘Data centre facilities and infrastructures - Part 99-1: Recommended practices for energy management’. The implementation of those practices should be verified by an independent third-party and audited at least every three years.
- The equipment used meets the requirements laid down in Directive 2009/125/EC for servers and data storage products. Currently this means the requirements in the ecodesign regulation for servers and data storage products (EU) 2019/424.
- The equipment used does not contain the restricted substances listed in Annex II to Directive 2011/65/EU of the European Parliament and of the Council, except where the concentration values by weight in homogeneous materials do not exceed the maximum values listed in that Annex (the RoHS Directive).
- A waste management plan is in place and ensures maximal recycling at end of life of electrical and electronic equipment, including through contractual agreements with recycling partners, reflection in financial projections or official project documentation.
- At its end of life, the equipment undergoes preparation for reuse, recovery or recycling operations, or proper treatment, including the removal of all fluids and a selective treatment in accordance with Annex VII to Directive 2012/19/EU of the European Parliament and of the Council (the WEEE Directive).
Whether the EU Taxonomy is mandatory for companies depends on different circumstances and obligations for different economic actors. However, companies of any size can use the EU Taxonomy on a voluntary basis to show investors and stakeholders in general whether they are carrying out or planning sustainable activities.
3.2.4 Data Centers (DE-UZ 228) – Blue Angel
The German Ministry of Environment and the German Federal Environment Agency have developed voluntary ecolabels for energy-efficient data centres: the environmental labels “Energy Efficient Data Center Operation” (DE-UZ-161) and “Climate Friendly Colocation Data Centers” (DE-UZ 214). These two sets of criteria have been consolidated into “Data Centers” (DE-UZ 228)
Blue Angel Data Centres (DE-UZ 228). Basic Award Criteria. Edition January 2023. Version 1. https://produktinfo.blauer-engel.de/uploads/criteriafile/en/DE-UZ%20228-202301-en-criteria-V1.pdf
In order to be awarded the Blue Angel, operators of data centres and information technology must comply with minimum requirements, and this must be verified by an independent auditor (mandated by the German Environment Agency). The environmental label for “Data Centers” may be awarded to those data centres that comply with criteria, which also includes a requirement on reuse management:
Reuse Management
In order to satisfy the guidelines for the avoidance of waste (see German Circular Economy Act (Kreislaufwirtschaftsgesetz § 6 waste hierarchy), the ecolabel aims to promote the reuse of information technology (servers and storage devices) after the end of their service life in the data centre. Information technology that leaves the data centre may not be scrapped or destroyed. The applicant must present a secure process for the deletion of data and a contractual agreement with a refurbishing company (maintenance and refurbishment). The servers may be donated free of charge to charitable organisations or also sold for a fee to professional refurbishing companies (e.g. the manufacturer).
Exemption: Data media that contain confidential information (“classified documents”) according to the General Administrative Provision for the Material Protection of Classified Information 25/34 DE-UZ 228 Edition January 2023 (accessible at: GMBl. 2018 no. 44–47, p. 826) or other sensitive data for which there is no secure and non-destructive deletion process available that meets the requirements of the Federal Office for Information Security (BSI) are exempt from this requirement.
3.2.5 Climate Neutral Data Centre Pact
Cloud Infrastructure Service Providers in Europe (CISPE) and the European Data Centre Alliance (EUDCA) have created a governance coalition known as the Climate Neutral Data Centre Pact. Signatories to the Pact may be trade associations representing data centre operators or companies
Climate Neutral Data Centre Pact (2021) states the requirements are:
- Energy efficiency, using PUE as a metric
- Matching electricity use by purchasing clean energy (clean energy)
- Setting and meeting ambitious targets for water usage effectiveness
- Increasing the quantity of server materials repaired or reused and creating a target percentage for repair and reuse (circular economy)
- Exploring possibilities to interconnect with district heating systems and other users of heat.
3.3 Standards
3.3.1 EU material efficiency standards
To support the implementation of material efficiency requirements within the framework of the EU Ecodesign Directive, various standards have been developed under the standardisation mandate M/543 from the European Commission especially targeting material efficiency aspects under the Ecodesign Directive. These are the EN 45552 to EN 45558 standards (the so-called EN 4555X series of standards).
In addition, a technical report CLC/TR 45550:2020 “Definitions related to material efficiency” was developed. The developed standards are shown in Table 7.
The standards include very detailed information regarding definitions, criteria, and assessment methods. For more information, please refer to the standards.
Reference | Topic |
EN 45550:2020 | Definitions related to material efficiency (technical report) |
EN 45552:2020 | General method for the assessment of the durability of energy-related products |
EN 45553:2020 | General method for the assessment of the ability to remanufacture energy-related products |
EN 45554:2020 | General methods for the assessment of the ability to repair, reuse and upgrade energy-related products |
EN 45555:2019 | General methods for assessing the recyclability and recoverability of energy-related products |
EN 45556:2019 | General method for assessing the proportion of reused components in energy-related products |
EN 45557:2020 | General method for assessing the proportion of recycled material content in energy-related products |
EN 45558:2019 | General method to declare the use of critical raw materials in energy-related products |
EN 45559:2019 | Methods for providing information relating to material efficiency aspects of energy-related product |
Table 7. Material efficiency standards for energy-related products
The material efficiency standards developed under M/543, are horizontal standards which cannot be directly applied to energy-related products or product groups. The standards provide general methodologies to assess different material efficiency aspects of energy-related products. The horizontal documents need to be adapted in order to be applicable for specific products/product groups.
Short descriptions of the standards are given below. The standards include very detailed information regarding definitions, criteria, and assessment methods, so the text below presents only very brief overviews. For more information, please refer to the standards.
CLC/TR 45550:2020: Definitions related to material efficiency (technical report)
Includes definitions of parameters and methods relevant for assessing durability, upgradability and ability to repair, reuse and re-manufacture of products". The technical report constitutes a collection of common terms used in deliverables prepared in accordance with M/543.
As such, the definitions in the report provide a single definition of key terms used in the material efficiency standards further described below.
Application
This standard is considered of high importance to ensure the consistent use of terminology in the EN 4555X series standards and in regulations based on these.
EN 45552:2020: General method for the assessment of the durability of energy-related products
This standard deals with parameters and methods for the assessment of reliability and durability of ErP (Energy-Related Products). It includes relevant terms and definitions and explains the key concepts to be considered.
Durability (of part or product): Ability to function as required, under defined conditions of use, maintenance and repair until a limiting state is reached. A limiting state can be changed to a functional state by maintenance and repair. Durability can be expressed in time (hours or years), number of operation cycles etc.
Examples of existing specific durability requirements are:
- the operational time for motors (expressed in hours) in the ecodesign regulation for vacuum cleaners.
- the minimum lifetime for hose (still useable after 40000 oscillations under strain) in the ecodesign regulation for vacuum cleaners.
Reliability: Probability that a product functions as required under given conditions, including maintenance, for a given duration without limiting events. Limiting events are for instance failure, wear-out failure, or deviation of any analogue signal. To assess reliability, the time at which a certain percentage of products has reached a limiting state is used.
An example of reliability requirements is the lamp survival factor for light sources:
- The lamp survival factor is the fraction of the total number of light sources that continue to operate at a given time under defined conditions and switching frequency (i.e. at least 9 light sources of the test sample of 10 units of the model must be operational after completing the test described in Annex V of the ecodesign regulation for light sources and control gears (EU) 2019/2020.
Application
Both durability and reliability requirements are very product-specific and closely connected to certain parameters of the product. Therefore, it will be necessary to develop/use product-specific requirements or test methods for certain relevant quality or performance parameters of the product. For instance, the proposed ecodesign regulation for mobile phones, cordless phones and tablets
See proposed ecodesign regulation for mobile phones (including smartphones), cordless phones and tablets here: https://ec.europa.eu/info/law/better-regulation/have-your-say/initiatives/12797-Designing-mobile-phones-and-tablets-to-be-sustainable-ecodesign_en. Be aware that the link does not show the final regulation.
EN 45553:2020: General method for the assessment of the ability to remanufacture energy-related products
Provides a general method for assessing the ability of an energy-related product to be remanufactured (refurbishment is not part of this standard). Remanufacturing is identified as an industrial process where at least one change is made to the product influencing its safety, performance, purpose or type of the product. The standard identifies seven process steps which are important to the remanufacturing process and identifies and provides general methods for evaluation of product characteristics which are linked to the possibilities for remanufacturing of the product.
The identified product characteristics (called attributes in the standard) are:
Ability to be identified as a product relevant for remanufacturing.
Ability to locate access points and fasteners covers aspects that can help locating key elements in relation to the disassembling and assembling of the product, such as access points, fasteners, diagrams showing locations etc.
Accessibility of parts dealing with how easy it is for operators to get access to the parts of the product, which need to be disassembled, or to be repaired, replaced, or upgraded.
Ability to be disassembled or assembled describes the ability of the product to be separated into its parts and of the parts to be assembled. Criteria are, among others, the number of operators needed and number of tools, and (different) fasteners to be used.
Wear and damage resistant during the remanufacturing process steps describes the ability of the product or its parts to withstand all the treatment that is needed during the remanufacturing processes without been damaged, for instance that materials and fasteners are strong, and that materials and markings can withstand cleaning agents.
EN 45554:2020: General methods for the assessment of the ability to repair, reuse and upgrade energy-related products
Provides a generic method to assess the ability of products, or parts thereof to be:
- reused (product or its parts have reached the end of their first life and are used again for the same purpose)
- repaired (process of returning a faulty product to a condition where it can fulfil its intended use)
- upgraded (process of enhancing the functionality, performance, capacity, or aesthetics of the product)
The following four steps should be carried out in order to define any product-specific assessment method:
- Determination of the priority parts to be included in the assessment, where a priority part is determined by its likelihood to need replacement or upgrading, its suitability for reuse or the functionality of the part.
- Identification of criteria and appropriate categories relevant for the assessment of all priority parts
- Assignment of a ranking/classification score to each category of relevant criteria for different priority parts and
- Specification of a calculation method to aggregate the results from the three previous steps for each priority part.
The identification of priority parts should take into account the analysis of EN 45552, where a list of failure parts is identified as part of the analysis. Where relevant, the list of priority parts shall be ranked in terms of enabling repair, reuse, or upgrade.
The below-listed criteria should be assessed to decide which of them are relevant for the product group in question. The list is non-exhaustive.
Product-related criteria:
- Disassembly depth
- Fasteners and connectors
- Tools
- Working environment
- Skill level.
Support-related criteria:
- Diagnostic support and interface
- Availability of spare part for repair/update
- Types and availability of information
- Return models for repair/upgrade
- Availability of parts for upgrade
- Spare parts availability by duration of availability,
- Availability of data deletion/transfer and to restore to factory setting
- Availability of software and firmware support including updates.
A number of methods for the assessments are described in Annex A to the standard. The methods include: example of scoring system for disassembly depth; classifications of fastener types, tools, working environment and skill level; classification by diagnostic support and interfaces; various classifications regarding spare part availability and availability of information; classification of return options and data management and password and factory reset. Additionally, a method for aggregation of criteria scores are represented.
Application
Parts of this standard have been used in the proposed ecodesign and energy labelling regulations for mobile phones, cordless phones, and tablets regarding disassembly requirements (requirements for fasteners, tools, working environment and skills). This shows that (at least) part of the standard is applicable for setting more detailed repair and disassembly requirements.
EN 45555:2019: General methods for assessing the recyclability and recoverability of energy-related products
Provides general principles for assessing the recyclability and recoverability of energy-related products. It elaborates on the product characteristics relevant for recyclability and recoverability of the product itself rather than the recycling or recovery processes.
The assessment of the recyclability/recoverability shall be based on the assumptions that the entire product undergoes the treatment in a selected reference end-of-life treatment scenario and that no preparing for reuse takes place. The scenario shall take into account the availability and efficiency of state-of the-art recycling and recovery processes to determine the recyclability/recoverability rate of an ErP.
The ability of the product to be recycled and recovered depends upon the following factors:
- the design characteristics of the product such as its structure, material composition, size, and mass
- the techniques, combination or sequence of techniques used to recycle or recover a given waste stream.
Marking of certain parts, which are separated during the recovery process, can facilitate selected recycling and recovery processes. Easy removal of certain parts does not necessarily increase recoverability if those parts are not removed in the reference end-of-life treatment scenario considered.
Critical Raw Materials (CRMs) generally have a negligible effect on the mass-based recyclability rate of the product, but may contribute towards reducing supply, economic and environmental risks and impacts. Therefore, the recyclability of CRMs shall be determined in accordance with a product-specific assessment.
When establishing assessment criteria for CRMs, the following aspects shall be considered:
- The potential presence of CRMs
- Distribution and concentration of CRMs across different parts
- Ability to access and remove parts containing CRMs
- Matters affecting possibilities to recycle CRMs.
The recyclability of CRMs may be assessed by the recyclability formula in the standard for those parts containing CRMs. A reference end-of-life treatment scenario and associated data for recycling and recovery factors of CRMs, must be defined.
The standard includes formulas for the calculation of the recyclability rate (Rcyc), and the recoverability rate, Rcov, of an ErP expressed in mass percent.
The calculation of the recyclability/recoverability rates for the entire product requires the determination of the recyclability/recoverability factors of all parts/materials of the product. However, the recyclability and recoverability rates can also be calculated only for specific parts/materials. The recyclability and recoverability rate for an individual material or for a part of interest, can be calculated as the ratio of the material that can be recycled/recovered, divided by the total mass of that material contained in the product or part.
Application
This standard is used as reference test method for calculation of the Rcyc in the proposed regulation for mobile phones, cordless phones, The end-of-life scenario to be applied is described in the regulation. See Annex IIIa regarding Transitional Methods. This shows that the standard is applicable if a relevant end-of life scenario is established for the product and its components/materials.
Due to the large uncertainties regarding data and the actual end-of-life scenario it seems more relevant to focus on specific parts/materials of interest than on entire products.
EN 45556:2019: General method for assessing the proportion of reused components in energy-related products
Provides general methods for assessing the proportion of reused components in an ErP. It deals with the assessment of the proportion of reused components on a generic level and it is intended to be used by technical committees when producing product-specific, or product group standards. Aspects like performance, validation, verification and suitability of reused components are not in the scope of the standard.
The calculation of the proportion of reused components can be applied at product level, by assessing each product on its own, or it can be based on a mass balance or number balance over a period of time. i.e.:
- Proportion of reused components calculated based on the mass of the reused components and the total weight of the product (in percentage)
- Proportion of reused component in the product by number calculated based on the number of reused components and the total number of components in the product (in percentage)
- As above but for mass and numbers for a defined period of time.
Formulas for the above calculation are included in the standard.
EN 45557:2020: General method for assessing the proportion of recycled material content in energy-related products
Describes a general method for assessing the proportion of recycled material in an energy-related product. It is applicable as the framework to be used for defining the assessment of recycled material content in specific product groups.
Recycled material is defined as material which either is pre-consumer material or post-consumer material. It has the same meaning as secondary material.
Pre-consumer material is material diverted from the waste generated during a manufacturing process excluding reutilization of materials such as rework, regrind or scrap generated in a process and being reincorporated in the same process that generated it.
Post-consumer material is material recovered from waste generated by households or by commercial, industrial and institutional facilities in their role as end-users of a finished product. This includes returns of products, or parts thereof, from the distribution of finished products for end-users.
Recycled material content is expressed as the average ratio of recycled materials used to the total production output of energy-related products over a specific period. The assessment of recycled material content requires:
- a description of the scope of the assessment
- a description of the material composition of a single product
- a management system to trace the type of material inputs, for both primary and recycled materials
- performance of a mass balance calculation, linking recycled material content of parts/products to total materials used in parts/products produced.
The standard describes how to determine the recycled material content of an ErP or its parts, as well as how to determine the recycled material content of a material, as manufacturers can sometimes be ErP manufacturers, part manufacturers and/or material manufacturers.
It is possible to perform the assessment of the ErP or parts thereof for
- all materials
- a type of material, e.g. plastic, metal, glass
- individual material, e.g. polypropylene, aluminum, float glass.
The scope of the assessment shall define whether the recycled material content assessment is done on the pre-consumer material or the post-consumer material or both.
More details of the assessment and calculation methods are included in the standard. The standard does also provide guidance for specific materials such as plastic, metals, and glass.
The verification of recycled material content relies on documented proof for traceability provided by the relevant operator in the CoC (chain of custody). The traceability system shall be able to track recycled materials from the moment they are identified as recycled materials to their final application. As a minimum, traceability information for the recycled materials is needed to calculate the recycled materials content.
Application
This standard is used as a reference test method in the proposed regulation for mobile phones, cordless phones and tablets, where it is required that manufacturers should provide information about the percentage of recycled content for the product or a part thereof (where available). See Annex IIIa regarding Transitional Methods. In the proposed regulation.
The standard seems to be more applicable to components or specific materials (for instance plastic) than for the entire product.
EN 45558:2019: General method to declare the use of critical raw materials in energy-related products
Proposes a standardized format for reporting use of Critical Raw Materials (CRMs). The main intention of EN 45558 is to provide a means for information on the use of CRMs to be exchanged up and down the supply chain and with other relevant stakeholders.
The standard does not provide any specific method or tool to collect CRM data. Process chemicals, emissions during product manufacturing and packaging are not in the scope of this standard.
The following definitions of critical raw materials (CRMs) are provided:
- Critical Raw Material: materials included in the Commission's list of Critical Raw Materials (European Commission, 2017a) and future updates to this.
- Regulated CRM: critical raw material for which a specific regulatory requirement has been set. Regulation could for instance be implemented via measures under the Ecodesign Directive.
- Non-regulated CRM: critical raw material for which no specific regulatory requirements have been set.
EN 45558 refers to the standard on material declaration EN IEC 62474, which is developed to facilitate the collection and declaration of information on the use of substances in products and product parts. It contains:
- a standardized list of declarable substances with standardized names to avoid misspelling (declarable substances list, DSL)
- a standardized format for declaration to ensure that declarations from different suppliers can easily be understood and exchanged.
The flexibility of the EN IEC 62474 declaration format enables the supply chain to effectively associate the CRM to both the product and to a specific part of that product.
Despite being developed for electrical and electronic equipment, EN IEC 62474 can be adapted to any type of industry as long as the substance list and the data exchange format follow the requirements stipulated in IEC 62474.
EN 45558 describes how to assess and declare the use of CRMs for both regulated and non-regulated CRMs. For regulated CRMs, a material declaration must be provided, and it should follow the specification in the applicable legislation. Typical requirements are:
- reporting of the name of the substance or substance group
- reporting the amount of the substance or substance group
- reporting the location of the substance in the product, if relevant
- exemptions, if applicable.
For non-regulated CRMs, it is voluntary to provide a material declaration. However, companies may still need to collect data on a CRM even if it is not regulated. In this case EN IEC 62474 can also be used. But as non-regulated CRMs are not automatically included in the Declarable Substance List, the manufacturers will need to create their own substance list. Examples of relevant information to be collected and assessed for non-regulated CRMs are:
- business information
- product information (e.g. product ID, name, category, weight)
- name of the substance or substance group
- amount of the substance or substance group
- Location(s) of the substance in the product
- Threshold for the reporting of the substance or substance group
Application
This standard is used as reference test method in the proposed regulation for mobile phones, cordless phones, and tablets. It was mentioned that EN 45558:2019 should be applied to gold following the same approach as for CRMs (even though gold is not on the CRM list). See Annex IIIa regarding Transitional Methods in the proposed regulation. This indicates that the standard can be applicable to broader group of materials than just CRMs.
EN 45559:2019: Methods for providing information relating to material efficiency aspects of energy-related products
Provides a general method for the communication of material efficiency aspects of energy-related products (ErP). It is intended to be used when developing a communication strategy in horizontal, generic, product-specific, or product-group publications. While the other standards in the EN 45552 – 45558 series provide methods to assess material efficiency aspects, this standard focuses on the communication of the various aspect-related information.
It describes a systematic approach for dealing with information linked to material efficiency requirements for ErPs within the framework of Ecodesign Directive. This includes, among others, identification of information to be mentioned (aspect-related content), target groups for the information, data sensitivity, and the means of communication and media to be used.
Application
This standard is of general nature and applicable to all ErPs.
Application of material efficiency standardETSI EN 303 808 v1.1.1 (2023-01) Applicability of EN 45552 to EN 45559 methods for assessment of material efficiency aspects of ICT network infrastructure goods in the context of circular economy. https://www.etsi.org/deliver/etsi_en/303800_303899/303808/01.01.01_60/en_303808v010101p.pdf
ETSI EN 303 808 v1.1.1 (2023-01) Applicability of EN 45552 to EN 45559 methods for assessment of material efficiency aspects of ICT network infrastructure goods in the context of circular economy. https://www.etsi.org/deliver/etsi_en/303800_303899/303808/01.01.01_60/en_303808v010101p.pdf
CLC/TC 59X has considered whether some of the standards could be more directly applicable for household and similar electronic appliances in the scope of the Ecodesign Directive and has concluded that EN 45558 regarding declaration of the use of critical raw material are directly applicable.
Use of the standards EN 45554:2020 (method for assessment of the ability to repair, reuse and upgrade of energy related products) and EN 45555:2019 (method for assessment of recyclability and recoverability of energy-related products) have been analysed in the context of the draft regulation on mobile phones, cordless phones and tablets (Schischke, et al., 2022). These standards explicitly mention that they are not intended to be directly applicable to individual product groups but require a further product group specific specification. The overall conclusion of the analyses is that the standards allow for setting both specific (i.e., threshold) requirements and generic (e.g., scoring) requirements.
The analyses conclude that, regarding EN 45554:2020, there is a tendency to pick specific elements from the standard and translate them into a specific requirement, for instance with regard to the type of fasteners, and requirements related to working environment and skills.
Regarding EN 45555:2019, relevant uncertainties related to the calibration of the reference end-of-life scenario were identified. And it is furthermore found that data points on exact material composition of products are very limited and frequently refer to end-of-life analysis. But still the standard is included in the proposed regulation for smartphones and slate tablets as a transitional test method.
ETSI has assessed whether the material efficiency standards EN 45552 to EN 45559 are directly applicable to ICT network infrastructure goods (ETSI, 2022).taking into account the specificities of ICT network infrastructure goods which include complex products designed for long operating lifetime, high availability and professional operation and maintenance processes in a business-to-business environment. It is concluded that the standard EN 45552 – EN 45555 is not directly applicable while EN 45556 – EN 45559 could be applied more directly – but may need smaller additions as outlined in clause 5 of the draft standard. The results are shown in Table 8.
With regard to EN 45558 General method to declare the use of critical raw materials it is conclude that:
Declaration of the use of critical raw materials is not specific for ICT network infrastructure goods compared to other EEE. Although different CRMs may be in focus for different ICT network infrastructure goods, as EN 45558 focuses only on declaration, it is not likely to need product-specific standardization.
Table 8. Summary of applicability of EN 45552 to EN 45559 standards to ICT network infrastructure goods (Source: ETSI EN 303 808 v1.1.1, 2023-01).
Reference | Title | Direct applicability | Product or product group specific standards necessary |
En 45552 | General method for the assessment of the durability | X | |
EN 45553 | General method for the assessment of the ability to remanufacture | X | |
En 45554 | General method for the assessment of the ability to repair, reuse, upgrade | X | |
En 45555 | General methods for assessing the recyclability and recoverability | X | |
En 45556 | General method for assessing the proportion of reused components | X | |
En 45557 | General method for assessing the proportion of recycled content | X | |
En 45558 | General method to declare the use of critical raw materials | X | |
En 45559 | Method for providing information relating to material efficiency aspects | X |
3.2.2 ETSI standards
ETSI is one the European standardisations organisations. The ETSI Technical Committee (TC) for Environmental Engineering (EE) develops standards for reducing the eco-environmental impact of Information and Communications Technologies (ICT) equipment.
This includes the following issues:
- the Life Cycle Assessment (LCA) of ICT goods, networks and services
- methods to assess the energy efficiency of wireless access networks and equipment, core networks and wireline access equipment including Efficiency metrics/KPI definition for equipment and network
- network standby mode for household and office equipment
- circular economy standard for ICT solutions
- Power feeding solutions based on higher DC voltage to reduce losses on the distribution cabling and innovative efficient storage solution.
ETSI has investigated current approaches, concepts and metrics of Circular Economy (CE) and Resource Efficiency (RE) and their applicability for the ICT infrastructure goods. The document ETSI TR 103 476
- introduction to CE and RE,
- description of CE as used in the ICT industry,
- description of existing CE and RE metrics and examples of their use,
- proposes next steps in CE and RE standardization.
ETSI is under Mandate M/573 working on standards to support the current ecodesign requirements for servers and data storage products regarding energy and resource efficiency.
Work items relevant for resource efficiency are:
- EN 303 800-2 DEN/EE-EEPS47-2: "Environmental Engineering (EE); Assessment of material efficiency of ICT network infrastructure goods (circular economy); Part 2: server and data storage product secure data deletion functionality".
- ETSI EN 303 800-3 DEN/EE-EEPS47-3: "Environmental Engineering (EE); Assessment of material efficiency of ICT network infrastructure goods (circular economy); Part 3: server and data storage product availability of firmware and of security updates to firmware".
- ETSI EN 303 800-5 DEN/EE-EEPS47-5: "Environmental Engineering (EE); Assessment of material efficiency of ICT network infrastructure goods (circular economy); Part 5: server and data storage product disassembly and disassembly instruction".
Adoption of the standards is expected in the second half of 2024
3.3.3 ITU standards especially relevant for servers and data storage products
International Telecommunication Union (ITU) aims to standardise practices regarding IT equipment. Several standards consider the circular economy and e-waste to achieve long-term sustainability ambitions.
ITU-T L.1xxx standards are focused on power supply series, e-waste management and recycling of rare metals in ICT products, which could be also adopted in DCI:
- Recommendation ITU-T L.1100 (2012): Procedure for recycling rare metals in information and communication technology goods,” (ITU, 2012). The standard provides information on the recycling procedures of rare metals in information and communication technology (ICT) goods. It also defines a communication format for providing recycling information of rare metals contained in ICT goods.
- Recommendation ITU-T L.1021 (2018): Extended producer responsibility – Guidelines for sustainable e-waste management (ITU, 2018a). The standard describes the extended producer responsibility (EPR). It expands on the different existing forms of EPR globally, not only in theoretical terms, but also with a practical view on their feasibility, challenges and prerequisites. It presents the definition of the EPR system, in addition to the roles and responsibilities of the different stakeholders and the different types of EPR, as well as how and why they could be used in certain contexts and not in others.
- Recommendation ITU-T L.1022: "Circular Economy: Definitions and concepts for material efficiency for Information and Communication Technology".
3.3.4 Data sanitation standards
Storage devices must go through data deletion, referred to as “data sanitisation”, before being reused. In general, sanitisation is defined as the process of eliminating sensitive information from a document or other medium (i.e. digital media such as HDDs and SSDs.).
Existing standards about data sanitation and deletion of hardware are gathered in Table 9.
Table 9. Existing standards about data sanitation and deletion of hardware. List taken from Blancco
Standard Name | # of Passes | Description |
Air Force System Security Instruction 5020 | 2 | Originally defined by the United States Air Force, this 2-pass overwrite is completed by verifying the write. |
Aperiodic random overwrite/Random | 1 | This process overwrites data with a random, instead of static, pattern. Each sector of the drive will contain different data. This process is completed by verifying the write. |
Blancco SSD Erasure | Proprietary | Blancco’s multi-phase, proprietary SSD erasure approach utilizes all supported SSD security protocols. This innovative method includes multiple random overwrites, firmware level erasure, freeze lock removal and full verification. |
Bruce Schneier’s Algorithm | 7 | This 7-step process, presented by security technologist Bruce Schneier, overwrites using 1s, 0s and a stream of random characters. |
BSI-2011-VS | 4 | This 4-pass system is the original BSI standard defined by the German Federal Office of Information Security. |
BSI-GS | 1 | Defined by the German Federal Office for Information Security, this process begins by removing hidden drives (HPA/ DCO if existing) and overwriting with aperiodic random data. The next step triggers a firmware-based command dependent on the type of drive. The last step is to verify the write. |
BSI-GSE | 2 | The BSI-GSE adds one extra step to the BSI-GS. After the first overwrite, an additional overwrite with aperiodic random data is added before moving on to the last two steps. |
CESG CPA – Higher Level | 3 | The UK government’s National Technical Authority for Information Assurance standard is a 3-pass process with a verification after each step. |
Cryptographic Erasure (Crypto Erase) | N/A | This method uses the native command to call a cryptographic erasure, which erases the encryption key. While the encrypted data remains on the storage device itself, it is effectively impossible to decrypt, rendering the data unrecoverable. Because this method uses the native commands as defined by the manufacturer, it is only available if supported by the drive being erased. |
DoD 5220.22-M | 3 | Published by the U.S. Department of Défense (DoD) in the National Industrial Security Program Operating Manual (also known as DoD document #5220.22-M), it specified a process of overwriting hard disk drives (HDDs) with patterns of ones and zeros. The process required three secure overwriting passes and verification at the end of the final pass. More on this standard is available at our blog, “Everything You Need to Know About the DoD 5220.22-M Disk Wiping Standard & Its Applications Today“. |
DoD 5220.22-M ECE | 7 | This method is an extended (7-pass) version of the DoD 5220.22-M. It runs the DoD 5220.22-M twice, with an extra pass (DoD 5220.22-M (C) Standard) sandwiched in between. |
Extended Firmware Based Erasure | 3 | This Blancco-defined standard adds an overwrite as the first step and then follows the standard Firmware Based Erasure, making this a 3-step process. |
Firmware Based Erasure | 2 | This Blancco-defined standard is a 2-step process triggers a firmware command that is dependent on the drive type. The last step of the process is to verify the write. |
HMG Infosec Standard 5, Higher Standard | 3 | Used by the British Government, this 3-pass overwrite adds one additional write. Like the baseline standard, this process is completed by verifying the write. |
HMG Infosec Standard 5, Lower Standard | 1 | Used by the British Government, this 1-pass overwrite consists of writing a zero pattern. This process is completed by verifying the write. |
IEEE 2883-2022 Clear | 0-2 | Developed by the IEEE Standards Association, IEEE Clear requires the removal/erasure of certain areas (such as hidden areas, depopulated storage elements, or cache zones, if existing). The data is then sanitized (via a firmware-based command or overwritten) and verified. To learn more, see our article, “New IEEE Data Erasure Standard Fills Technology Gap“ |
IEEE 2883-2022 Purge | 0-2 | Developed by the IEEE Standards Association, IEEE Purge requires the removal/erasure of certain areas (such as hidden areas, depopulated storage elements, or cache zones, if existing). The data is then sanitized (via a firmware-based command) and verified. To learn more, see our article, “New IEEE Data Erasure Standard Fills Technology Gap“ |
National Computer Security Center (NCSC-TG-025) | 3 | Defined by the US National Security Agency, this 3-pass system includes a verification after each pass of 0s, 1s and a random character. |
Navy Staff Office Publication (NAVSO P-5239-26) | 3 | Published by the US Navy, this 3-pass system uses a specified character (and its complement) and a random character. The process is completed by verifying the write. |
NIST 800-88 Clear | 0-2 | The National Institute of Standards and Technology Clear requires the removal of hidden areas (HPA/DCO, if existing). The data is then overwritten and verified. |
NIST 800-88 Purge | 0-2 | This method requires the removal of hidden areas (HPA/DCO, if existing). A firmware-based command is triggered depending on the type of drive, and the last step is the verify the write. Our NIST Guide gives more detail. |
3.3.5 Plastics
In August 2022, the European Commission notified to CEN and CENELEC the new Standardization Request on plastics recycling and recycled plastics, in support of the European Strategy for Plastics in a Circular Economy (M/584) (CEN & CENELEC, 2023).
The Standardization Request mandates CEN and CENELEC to revise eleven European Standards and develop around 45 new deliverables. Topics covered by the request include quality grades for sorted plastic waste, characterisation of recyclates, and design-for-recycling guidelines for a wide range of products used in different applications – such as packaging, construction, electronic and electrical equipment, road vehicles, and agriculture.
The work will involve seven CEN Technical Committees and two CENELEC Technical Committees. CEN/TC 249 ‘Plastics’ will be revising and developing most deliverables, including a standard on quality grades for sorted plastics wastes (HDPE, LDPE, PP, PET, PVC, PS, EPS) and a standard on quality assessment of plastic recyclates for use in products (rHDPE, rLDPE, rPP, rPET, rPVC, rPS, rEPS, rABS).